How Can a Penetration Test Help You?
HOW WE HELP
Comprehensive Security Assessments
Network Penetration Testing with Cyology Labs' Affordable, Accurate, and On-Demand
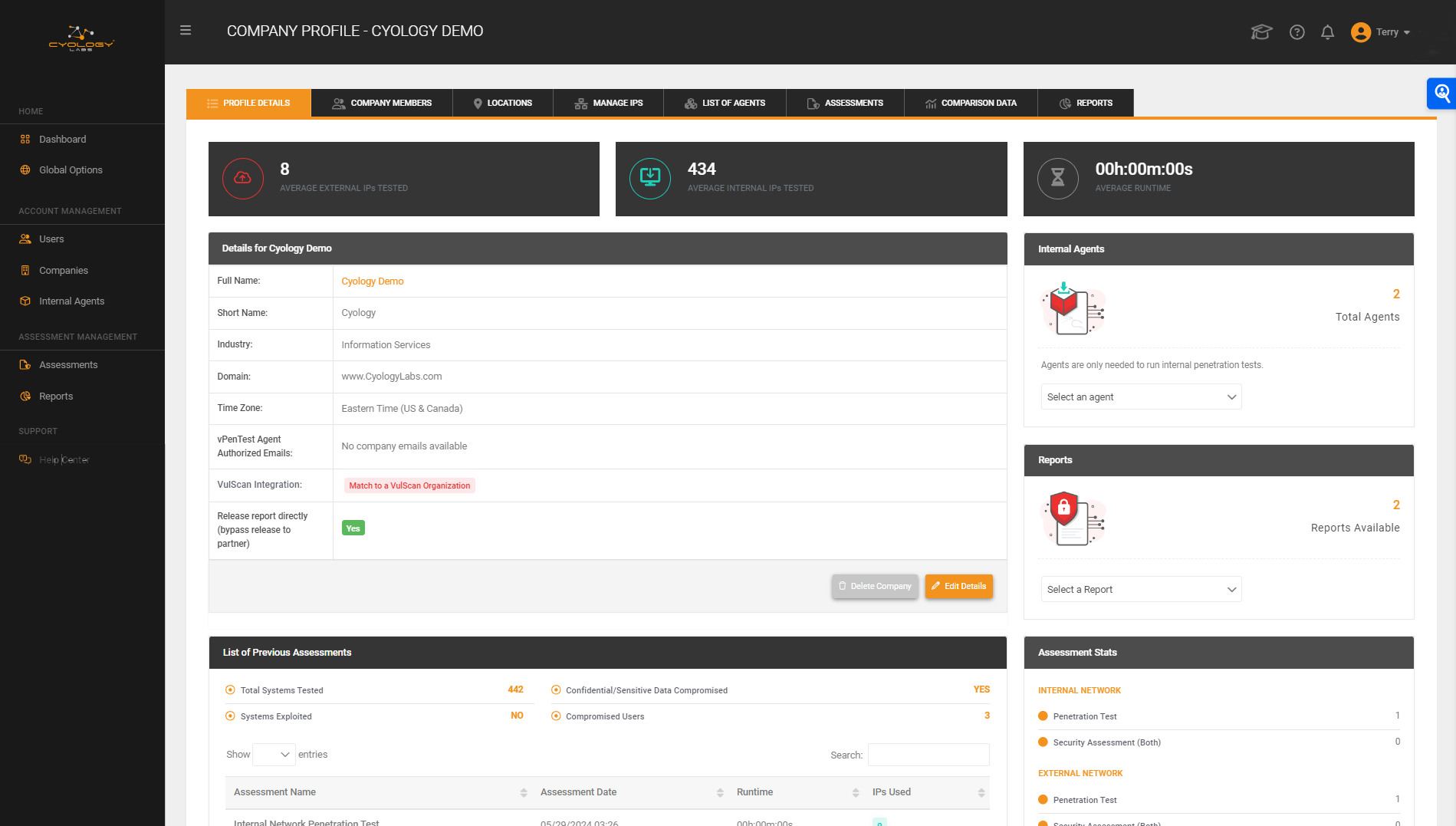
At Cyology Labs, we understand that security isn’t just about running scripts, it’s about combining technology with human expertise. Our continuous penetration testing platform offers the perfect blend of efficiency and insight, identifying vulnerabilities quickly and cost-effectively. But we don’t stop there.
Behind every scan, our seasoned security professionals dive deeper, analyzing complex threats and providing personalized recommendations tailored to your unique needs.
Our approach ensures you get the best of both worlds: the speed and thoroughness of automation, paired with the strategic thinking and creativity that only experienced experts can provide.
With our hybrid solution, you’re not just getting a test, you’re getting a comprehensive, actionable security assessment that drives real results.
Cyology Labs Solves Today's
CHALLENGES
Traditional methods for finding a qualified vendor for network security assessments can be time-consuming and challenging. At Cyology Labs, we streamline this process with our comprehensive approach, providing quality deliverables that clearly communicate identified vulnerabilities, their associated risks, and remediation strategies from both technical and strategic perspectives.
Companies face some of the following challenges when looking for a qualified vendor:
🔸 Finding an available vendor for security assessments..
🔸 Ensuring consultants have advanced experience.
🔸 Maintaining consistent and frequent communication.
🔸 Avoiding vendors that mislabel vulnerability assessments as penetration tests.
🔸 Receiving quality reports that effectively communicate risks and remediation steps
Our Solution:
Over the past five years, we’ve developed solutions that offer better, faster, and more cost-effective services, addressing all these challenges efficiently.
ON-DEMAND RISK MANAGEMENT
Conduct monthly or Quarterly security assessments to understand your risks to cyber attacks in near real-time.
Traditional assessments often provide only a point-in-time snapshot of an organization's security environment. At Cyology Labs, we offer continuous risk management solutions. Our platform enables monthly or on-demand security assessments, allowing organizations to efficiently conduct comprehensive evaluations. This approach measures the effectiveness of compensating controls through advanced exploitation techniques while minimizing risks by implementing strategic controls.
COMPLIANCE READINESS
Meet compliance requirements with more scheduling flexibility and real-time alerts.
Cyology Labs offers flexible scheduling and real-time alerts to help meet compliance requirements. Our platform provides real-time activity tracking and segmentation testing to ensure the isolation of sensitive networks. Beyond compliance, we also identify security deficiencies and deviations from best practices, ensuring your organization maintains a robust security posture.
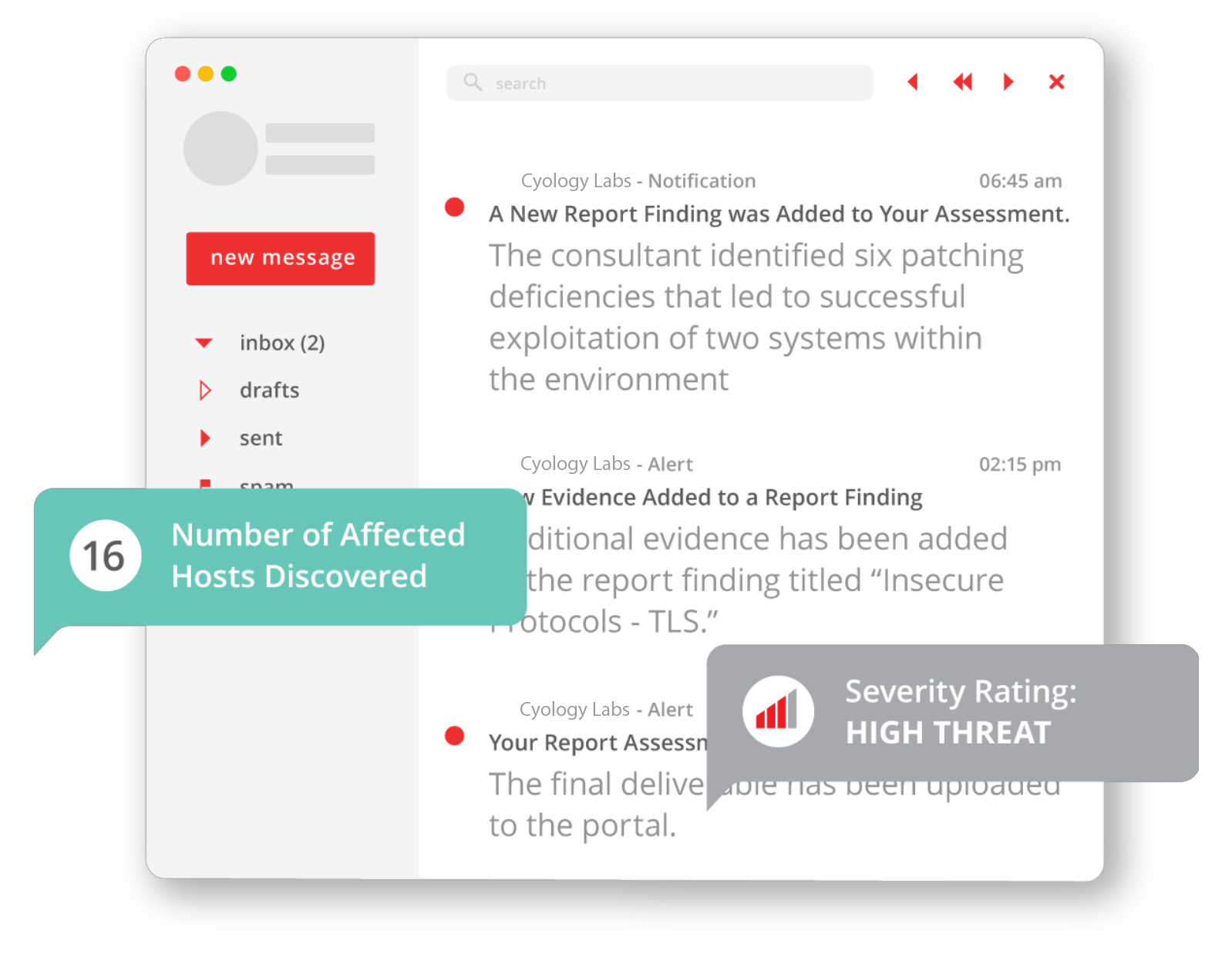
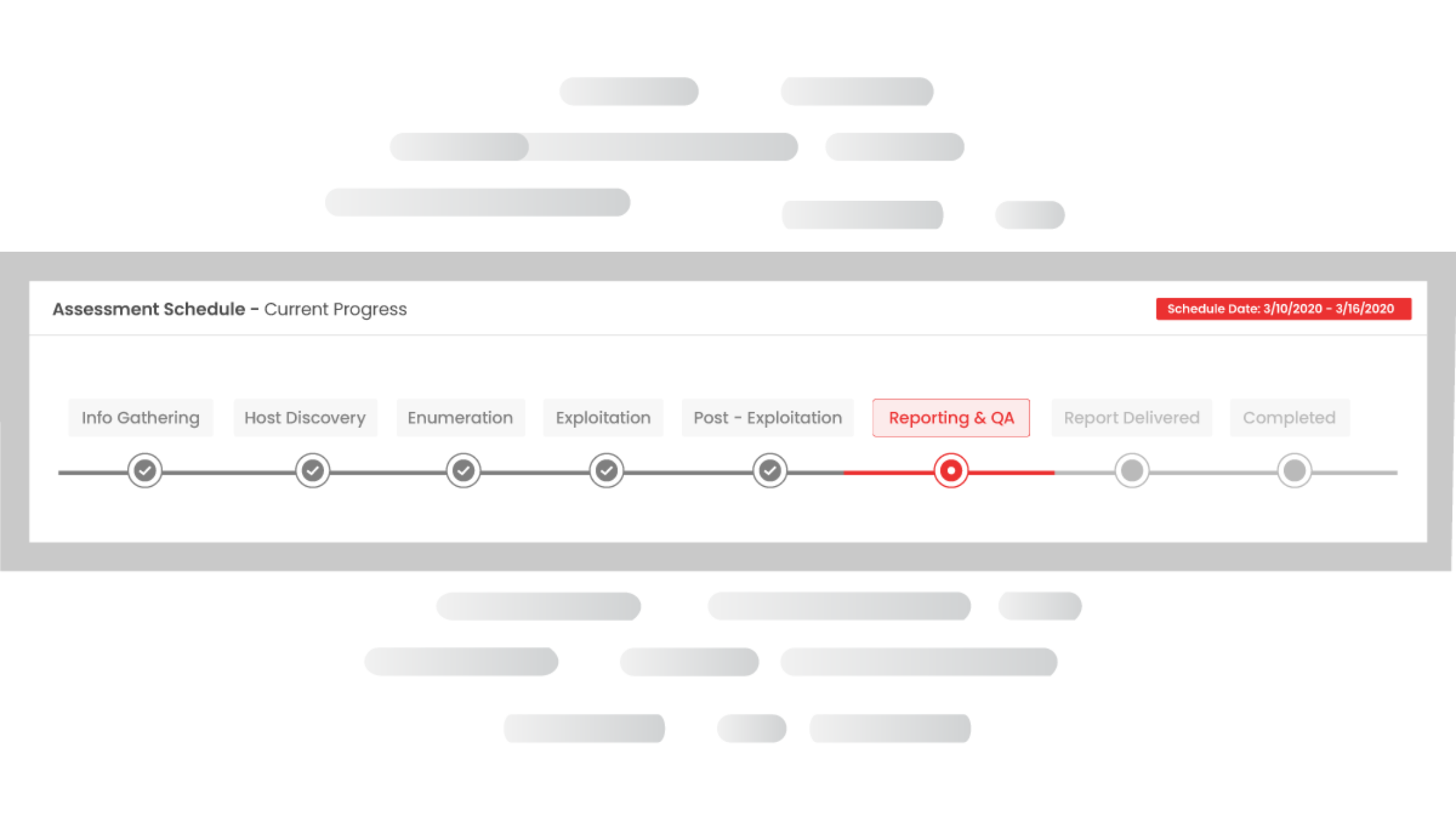
ALWAYS BE IN THE KNOW
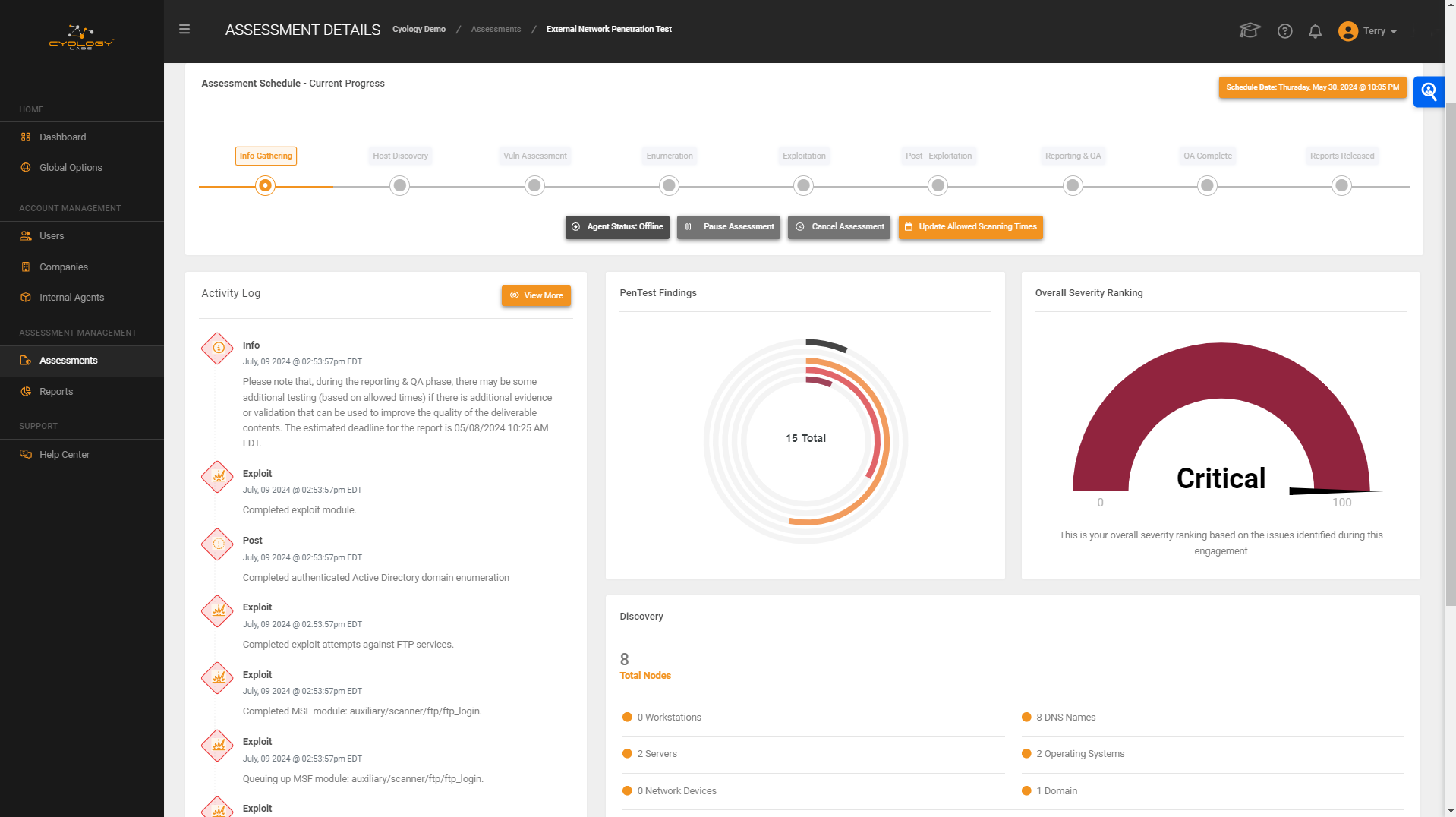
Track the progress and results of your penetration test in real time.
Our progress tracker ensure that your IT team knows exactly what the progress is of the engagement, when it’s expected to be completed, as well as any preliminary findings that we’ve identified. Your team will always know when and what activities are taking place. Each time a phase is completed, you will receive an email notification.
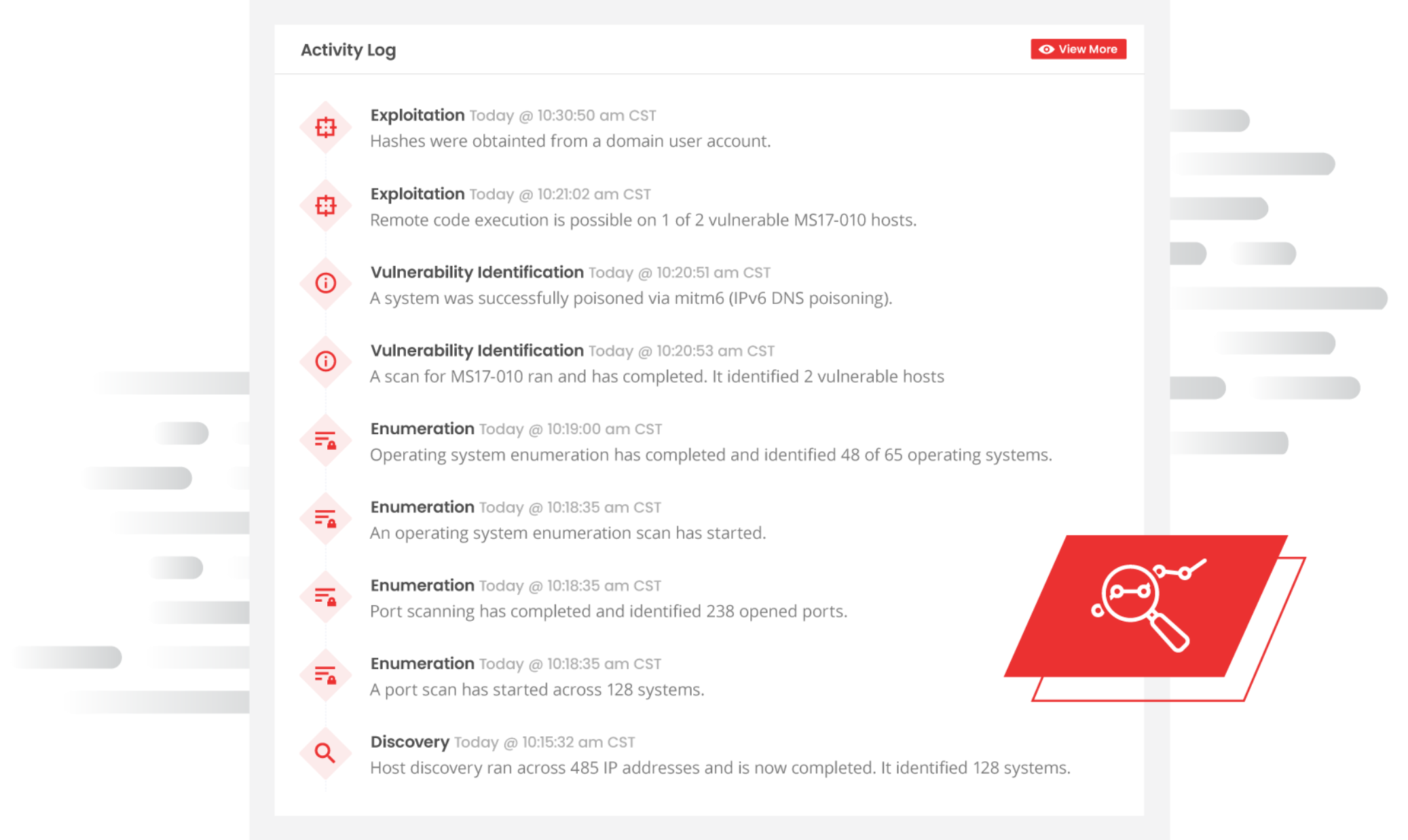
VALIDATE YOUR SECURITY CONTROLS
Ensure your security controls are working with our Activity Log.
To maximize the value of our penetration tests, Cyology Labs includes an activity log that tracks all activities performed during the assessment. This allows your network teams to correlate our actions with their SIEM and incident response procedures. Every engagement effectively functions as a collaborative assessment, enhancing both security testing and team coordination.
PRE- AND POST-BREACH SIMULATION
Cyology Labs can perform pre- and post-breach simulations at any time within both the internal and external network environments

Open Source Intelligence Gathering - Using information from the public Internet to contribute to a successful attack against the environment, including employee names, email addresses, etc.
Host Discovery - Performing discovery of systems and services within the environment targeted, and including active systems and port scanning.
Enumeration - Enumeration of services and systems to identify potentially valuable information, including vulnerability analysis.
Exploitation - Using information gathered from OSINT, host discovery, and enumeration, Cyology Labs also launches attacks against vulnerable services, including password-based attacks, man-in-the-middle (MitM) attacks, relay attacks, and more.
Post-Exploitation - After gaining an initial foothold on a system, Cyology Labs automatically attempts to launch privilege escalation attacks. New attack avenues will also be analyzed to determine if more access into the environment or sensitive data could be established.
Backed by Experience
Our platform is backed by experts with over 10 years of experience, holding certifications ranging from CISSP, eCPPT, OSCP, OSCE, CEH, and more. We have conducted hundreds of security assessments for hundreds of clients within various industries, and we’ve taken the most valuable strengths and combined them into a platform that allows our customers to have high quality assessments performed at their own convenience.
Penetration Testing Services include:
-
External Infrastructure Testing
The external infrastructure is the Web servers, Domain Name Servers, email servers, VPN access points, perimeter firewalls, routers, etc. that are publicly accessible from the Internet. Commonly the external infrastructure is considered to be the main target of attacks. Possible attackers are both human hackers as well as automated worms. It is vital for any business to guard itself against unwanted intruders and attackers while at the same time continue serving customers as well as other modern business needs.
-
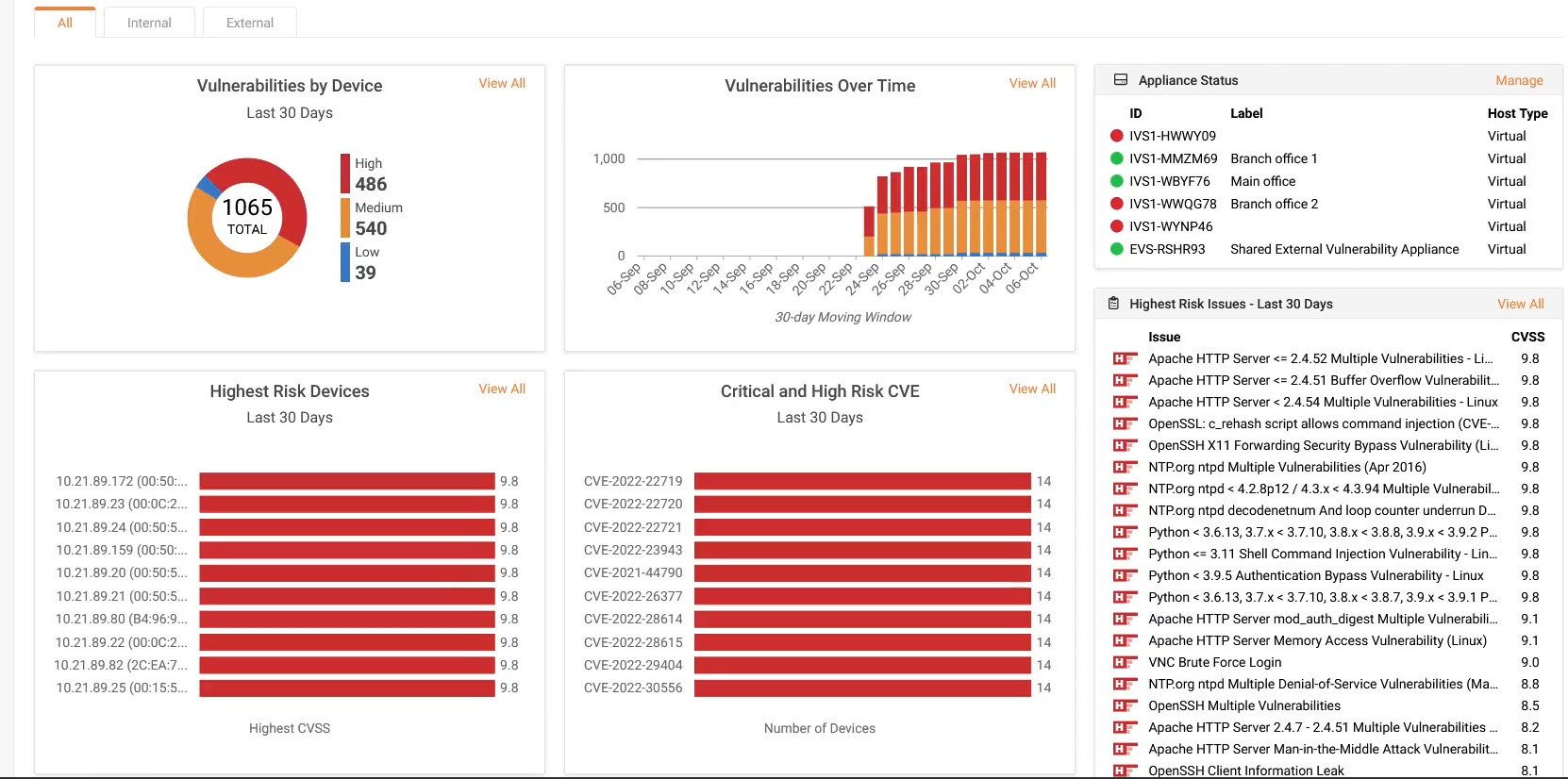
Continuous Vulnerability Assessments
A Vulnerability Assessment is an continuously scheduled task that provides a basic to an advanced overview of the client’s external or internal infrastructure. Cyology Labs makes sure all reports have been double-checked by one of our skilled professionals, therefore providing accurate Vulnerability Assessment reports.
-
Internal Infrastructure Testing
It is vital for any organization to be equally aware of the threats internally as well as externally. It is unfortunate, but even inside the safe work environment threats do exist for the IT infrastructure of most organizations and have surpassed external threats. Viruses, Worms, Trojans and disgruntled employees are a danger to the inner workings of a corporation. As modern networks get more diverse and multi-layered, it’s common for a number of issues to exist internally that could prove disastrous, varying from accidental incidents to corporate espionage.
Other Penetration Testing Services Available:
-
(WEB) Application Testing
For the past few years and even more so now with the introduction of what is known as “Web 4.0″, more and more applications are moving online, and are increasingly becoming the targets of malicious attackers. All of our testers are experts in various programming languages and web technologies that can investigate and detect issues with both online and off-line applications before an attacker does. This vulnerability assessment includes the connection requests to the databases, dynamic forms, users sessions, authentication and authorizations management, etc.
-
Wi-Fi SSID Pentest
A Wi-Fi pentest is an integral part of an organization's cybersecurity strategy, as it helps in identifying and mitigating potential risks in wireless networks, which are common entry points for attackers.
-
O365 Penetration Test
Cyology Labs works with clients to determine which security services and controls are currently in place, and which ones need to be in place to ensure the security and privacy of client data.
The 3-phase assessment of the O365 implementation includes the following:
-
Configuration assessment of O365 settings;
-
Validation of the configuration to determine if malicious payloads can be delivered by O365
-
Documentation
-
Application developers work under intense pressure, meeting customer demands for featureful, fast, highly-functional products on relentlessly tight schedules. But complexity is the enemy of security. Complex products need extra assurance that they can survive the hostile environments they’ll be deployed in.
Cyology Labs will assess the products that you build. Unlike other firms, members of our team can efficiently inspect shrink-wrap applications and appliances, and find vulnerabilities in products before they ship or hit Bugtraq. We provide security acceptance testing prior to releases and can help you build security into your development lifecycle during design, development, and testing.
Cyology Labs Assessments help vendors take control of software security by:
- Eliminating expense and schedule slip from security “dot releases”
- Set the terms on which vulnerabilities are found and resolved
- Transform software security from a liability to a competitive advantage
Or call us today at 1-844-CYOLOGY to learn more.
CONNECT ON SOCIAL MEDIA
Don't Wait Until It's Too Late To Be Up To Date. Download Fraudster On Your Mobile

Contact Us at 1-844-CYOLOGY
© Copyright 2024 Cyology Labs & TerryCutler.com . All Rights Reseved.